Resources
Mythos and LLMs changed the game, but we can now move the playing field. The disclosure of the Claude Mythos Preview in April 2026 fundamentally shatteredthe traditional cybersecurity paradigm. With expert analysis from CSA, SANS, andOWASP documenting a collapse in...
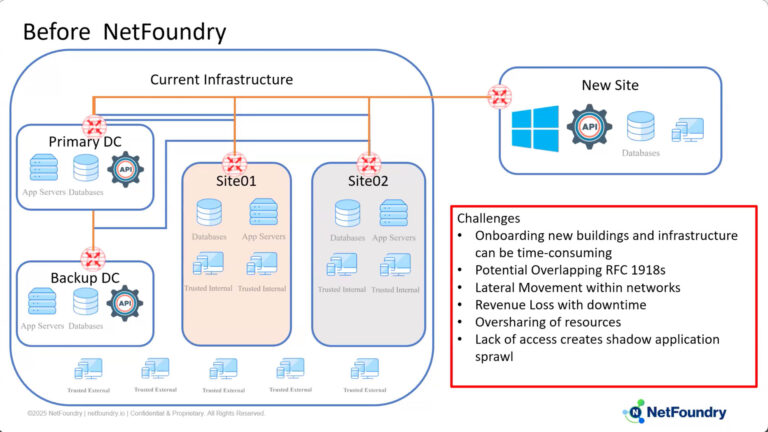
NetFoundry flipped the model from “network security” to “secure networking” Business networks (TCP/IP) don’t enforce strong identities, continuous authentication and fine-grained, deny-by-default authorization and access. They are by default insecure, expensive to manage and blockers to business velocity. The solution...
Accelerating DTM-25-003 Outcomes with Identity-First, Authenticate-Before-Connect Networking In modern OT, the challenge is no longer just how to connect systems securely, but how to do so without triggering repeated firewall/VLAN changes, MOC cycles, safety reviews, and IT/OT governance friction. This...
Secure and Accelerate Agentic AI Deployments Without Infrastructure Delays Agentic AI systems are inherently distributed and dynamic. AI agents interact with LLMs, MCP servers, APIs, and data services that may reside across multiple clouds, on-prem environments, or third-party platforms. These...
Accelerating DTM-25-003 Outcomes with Identity-First, Authenticate-Before-Connect Networking DoD components are under a clear mandate to achieve, at minimum, target-level Zero Trust across unclassified and classified systems (including national security systems) on the DoDIN by the end of FY2027, with priority...
NIST 800-207 outlines a framework where trust is never granted implicitly based on physical or network location. NIST Special Publication 800-207 is generally considered the most widely respected and authoritative definition of Zero Trust. It fundamentally redefines enterprise security by...
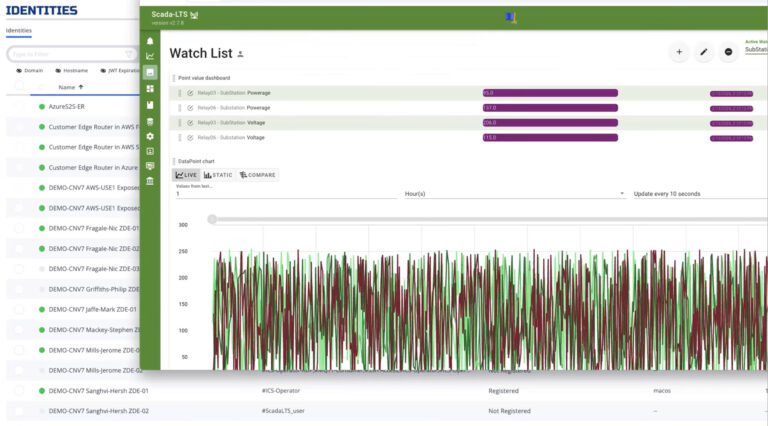
Enable OT Connectivity and Segmentation Without Compromising Safety, Uptime, or IEC 62443 Requirements Operational Technology (OT) systems need more connectivity – for vendor support, condition monitoring, analytics, and IT/OT integration – but traditional network-centric approaches (VPNs, jump servers, inbound firewall...
Accelerate Deployments and Eliminate Cyber Exposure Distributed workloads, such as those that enable modern applications, industrial devices and AI Agents, are aheadache for operations—and a dream for attackers. As enterprises deploy workloads across hybrid, multi-cloud, edge, OT, IoT, and partner...
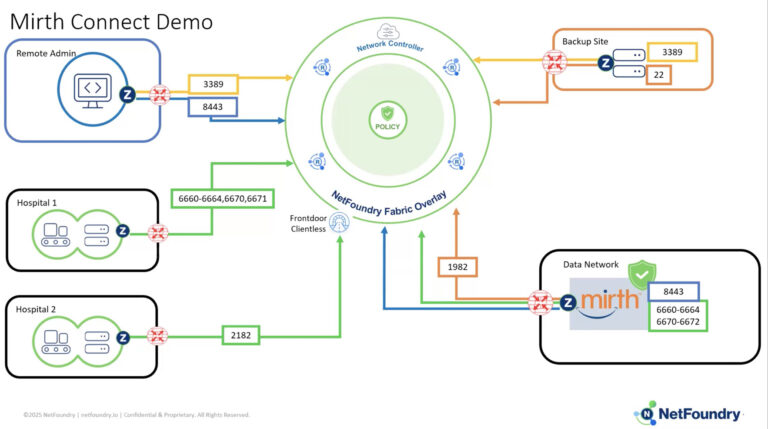
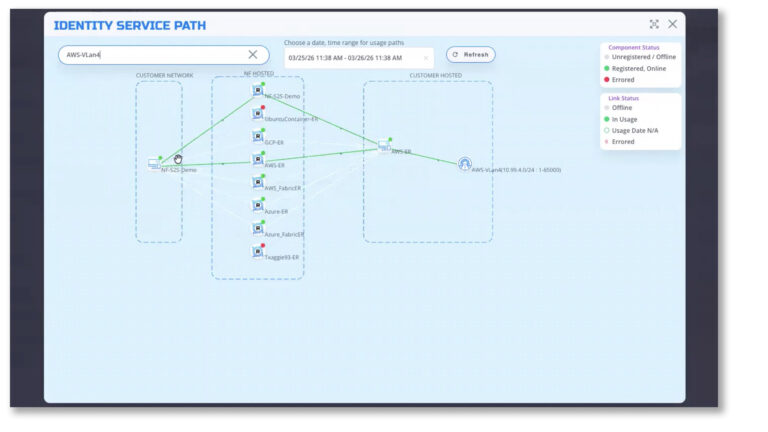
Accelerate Secure Customer Deployments Software and service providers increasingly need secure connectivity into customer IT, OT, IoT, and cloud environments—for application delivery, managed services, monitoring, support, and service-to-service communications. Yet traditional networking approaches introduce new operational activities and issues that...
NetFoundry White Papers Executive Summary In today’s interconnected digital world, Application Programming Interfaces (APIs) play a crucial role in enabling data exchange and service integration across organizations. As their usage expands, APIs are increasingly becoming targets for cyberattacks, especially when...
NetFoundry Case Studies KEO KEO International Consultants, a global leader in architecture, engineering, and project management, has been at the forefront of delivering iconic projects for over 57 years. Ranked among the top international firms by ENR and World Architecture,...