Every AI · Every API · Every Connection — Secured.Secure Your Workloads with Identity-First Reachability™
Stop managing your attack surface. Eliminate it—with the only identity-first zero trust fabric for every machine-to-machine interaction.


More than 3,000 organizations trust NetFoundry. Shouldn’t you?
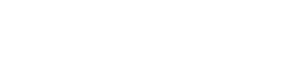
Cyberattacks Exploit Reachability
- Vulnerability exploitation has become the #1 breach vector, ahead of phishing and credential abuse combined. Source: 2026 Verizon DBIR
- Patching or adding ACLs can’t be done fast enough.
- AI agents, MCPs, LLMs, APIs, and IT&OT expand attack surfaces, creating risk and slowing deployments.
30 billion devices can scan, connect to, and exploit your attack surface.
AI Systems Intensify the Problem
- AI agents discover and interact with tools.
- MCP servers and APIs are broadly reachable.
- Secrets and API keys proliferate.
- Teams lose visibility and governance.
- Changes to infrastructure slow deployments.
- Employees use unauthorized AI tools.
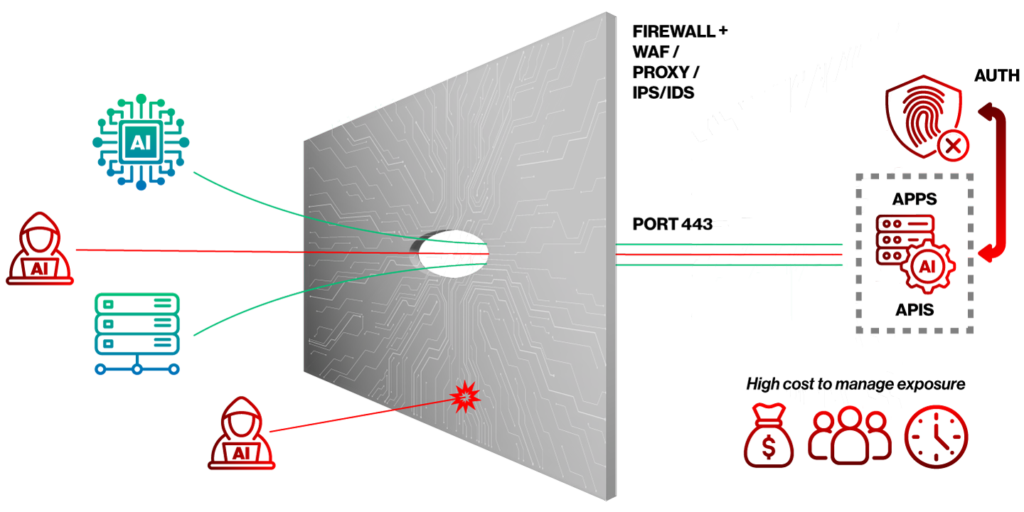
Make Attackers Fight Blind withIdentity-First Reachability™
- Eliminate reachability that attackers exploit and defenders struggle to secure.
- MCPs, LLMs, APIs, and IT/OT/IOT sites are invisible until their machine identity is authorized, securing them from attackers and AI agent misuse.
- The only identity-first zero trust fabric for every machine interaction.
Every AI, Every API, Every Connection — Secured.
- Deploy at software speed.
- Stop wasting time on never-ending firewall rule changes and site-to-site VPNs.
- Get workload visibility and governance based on unique machine identities.
- Deploy any workload across any boundary.
Proven Simplicity
NetFoundry secures billions of sessions for critical infrastructure on three continents and multiple Fortune 10 companies, supporting HIPAA, CJIS, PCI, EU CRA, NIS-2, NERC CIP, IEC 62443, NIST 800-171, DORA, and FedRAMP. Spin up a secure dedicated network in minutes, with no hardware dependencies, as easily as a VM or container.
Zero Trust AI Enclaves
Secure your AI deployments without slowing them down
Route AI clients to tools and models through a dedicated, private connection with cryptographic identity, end-to-end encryption, no shared API keys, no open ports, and no VPN.
- One Identity, one security model
- Coordinated governance and correlated observability
- Cost (tokens) and security controls
Zero Trust API Security
Secure APIs without exposing infrastructure
Make APIs invisible until access is authorized, eliminating 99.99% of the threat to your API attack surface.
- Simplified with identity-based governance and observability
- Agent and agentless options to cover every use case
- The only way to securely publish public APIs without an API gateway, while also blocking lateral movement
Zero Trust IT & OT Connectivity
Simplify site connectivity and micro-segmentation
Achieve universal IT/OT/IOT connectivity with less risk at lower cost.
- Simplify universal site access and micro-segmentation
- No VPN or ongoing firewall updates
- Zero-trust access based on identities and services
3000 companies use NetFoundry
8 of 10 largest US banks connect users to data with NetFoundry
1B+ sessions/month across global redundant infrastructure
Who Doesn't Love Simple & Secure?
Learn More


Talk With Us
Learn more about securing workloads with Identity-First Reachability™