AI Deployment and Protection Secure Your AI Deployments Without Slowing Them Down
- Deploy a secure, zero trust enclave for your users, AI agents, MCP servers, and LLMs.
- Avoid wasting time on never-ending firewall rule changes.
- Centralize AI cost accounting and optimization.
Want to learn more?
MCP Gateway + LLM Gateway. Identity-First Reachability™ for AI.
AI tools need access to internal resources, models, and APIs. Traditional approaches force a choice between security and velocity. These gateways eliminate that tradeoff.
One identity, one security model
Both gateways are built on OpenZiti and share the same zero-trust foundation. They work independently, but they’re designed to work together.
Let’s Talk >>
Secure and Govern LLM and MCP Resources Via a Single, Unified AI Platform
- A separate, zero trust enclave for all components of your AI deployment
- No open inbound firewall ports; no network changes, no VPNs required
- Strong identity-based and authentication for AI agents that’s simple to set up, operate, audit
- AI agents and MCP servers have no access to API keys and service accounts
- AI token tracking for cost optimization, accounting, and limit setting
- LLM routing and multi-model load balancing support
Deploy AI Quickly and Manage Changes Effectively
- Simple—no open inbound ports
- Fast deployments—no network or firewall changes required
- Works in both internally- and externally-controlled environments
- Optionally build directly into AI components (via SDK)—network as code
- Can leverage NetFoundry’s existing routing fabric if desired
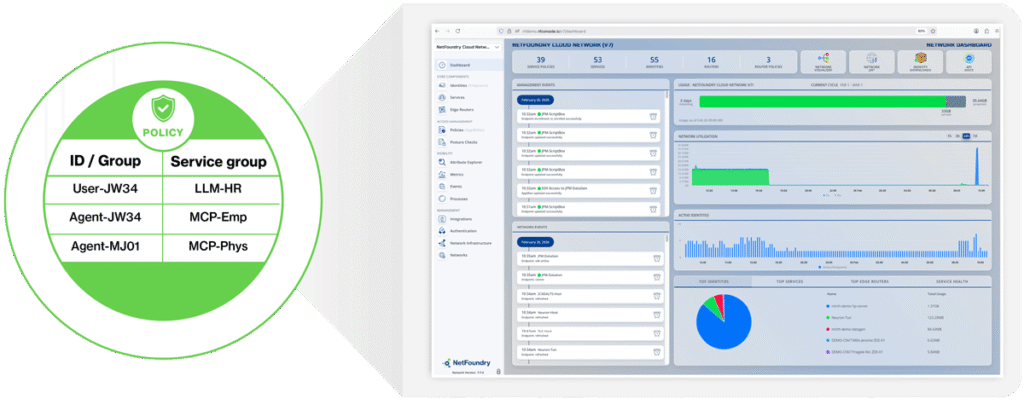
Identity-Based Visibility and Control for AI Connectivity
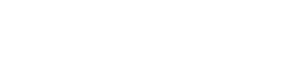
- All connectivity managed by policy, not network changes
- Just-in-time programmatic policy changes apply instantly and can have limited duration.
- Visibility and auditing based on identity, not cumbersome IP addresses
Secure Your AI Deployments Without Slowing Them Down
Without NetFoundry: AI Resources Are Exposed on the Network
- Risk of attacker API exploitation, token theft and impersonation (OWASP Top 10)
- Ongoing firewall change management headaches
With NetFoundry: AI Resources Are Not Exposed on the Network
- 99% risk reduction by eliminating unauthorized network connections
- Simplified non-human access control and audit by identity, and elimination of firewall rule changes
AI Challenges and NetFoundry Solutions
AI Challenges | NetFoundry for AI Solutions |
|---|---|
Agents, MCP servers, and LLMs increase the attack surface area | NetFoundry provides an AI enclave with no open ports available to a potential attacker—it’s invisible |
AI agents and MCP servers lack strong identity | NetFoundry provides the identities |
AI agents host critical API keys and tokens that are potential targets of an attack | NetFoundry hosts them separately and securely |
AI deployments are fluid and highly distributed, so depending on network changes isn’t feasible | NetFoundry doesn’t depend on the network configuration—it doesn’t even require any open inbound ports. So no network changes are required. |
AI deployments are difficult to visualize and to audit | NetFoundry provides identity-based visibility and audit |
Flexible NetFoundry Deployment Options
Open Ziti
Self-Hosted Open Source
- Community support
- Self-deployed and managed (connectors, routers, controller), self-orchestrated
Self-Hosted
Self-Hosted Licensed
- Enterprise-grade support (24×7)
- Self-deployed and managed (connectors, routers, controller), self-orchestrated
- Guidance for resilient, reliable, scalable production architecture and deployment
- Operations, logging, assurance, and platform LCM tools
- Contracted relationship (indemnification)
- FIPS compliant
- Use case and/or implementation documentation
Cloud
SaaS
- Enterprise-grade support (24×7)
- Fully managed by NetFoundry with 99.95% uptime SLA
- Guidance for resilient, reliable, scalable production architecture and deployment
- Fully automated LCM of hosted components; LCM support for self-hosted components
- Contracted relationship (indemnification)
- FIPS compliant
- Use case and/or implementation documentation
- SOC 2 Type II compliant
Simple to deploy, simple to operate, and eliminates 99.99% of exploitation risk