Blog
I recently had the opportunity to participate in the creation of the third version of the Cloud Security Alliance’s “Deep Dive into...
This roadmap provides a phased, 150-day timeline to eliminate exposure across all vital categories, including B2B APIs, OT/ICS networks, third-party vendor tunnels,...
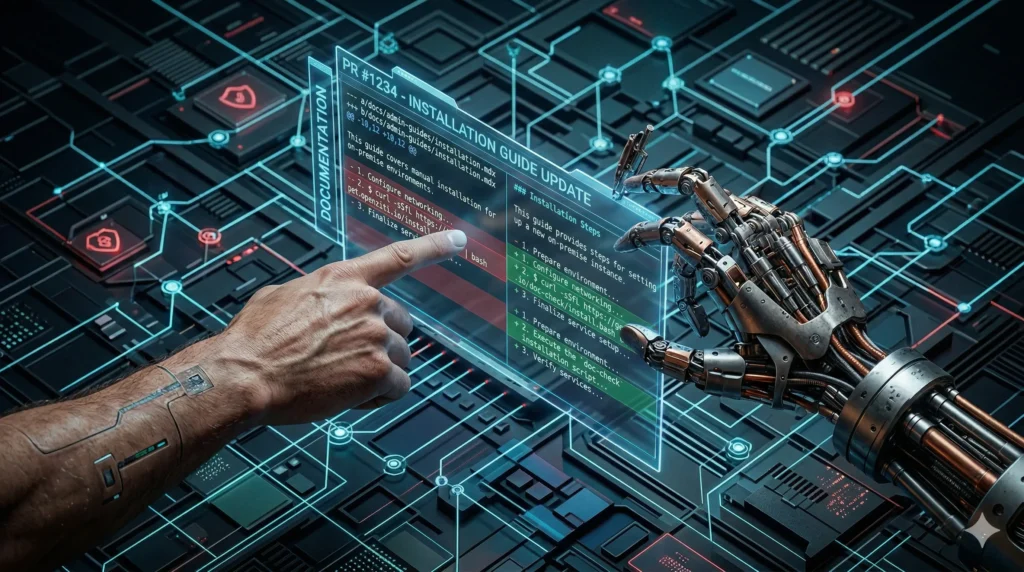
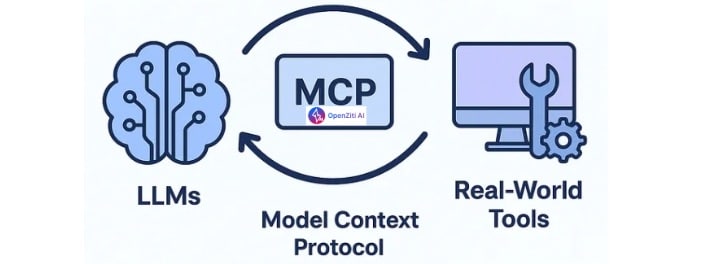
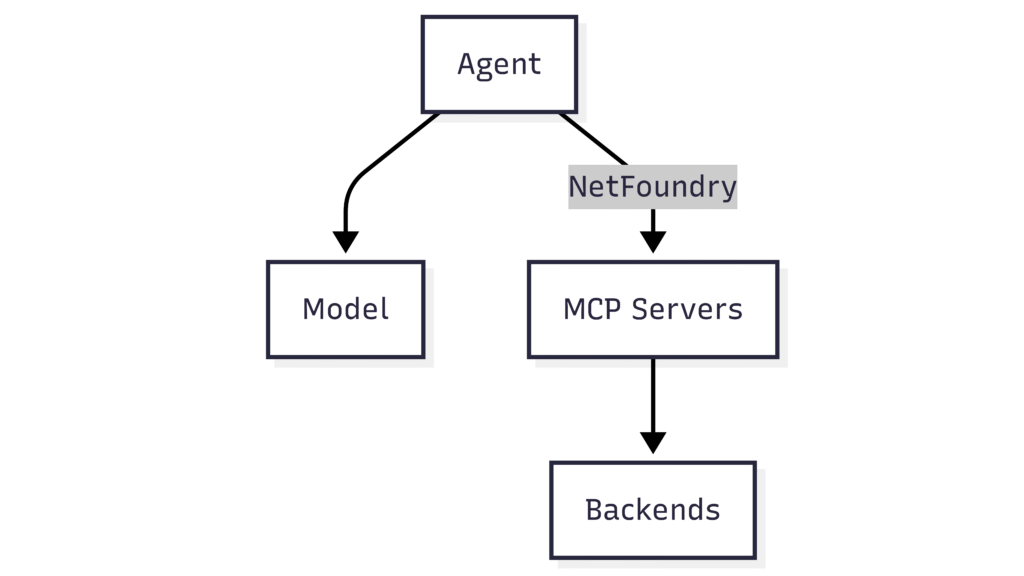
A content orchestrator series for the modern technical writer At NetFoundry, we’re building the foundational architecture for zero-trust networking with OpenZiti (our programmable zero-trust overlay)....
Recently I had the chance to speak at the 4th Annual DoW Zero Trust Learning Exchange, a collaboration between ATARC, DAU and...
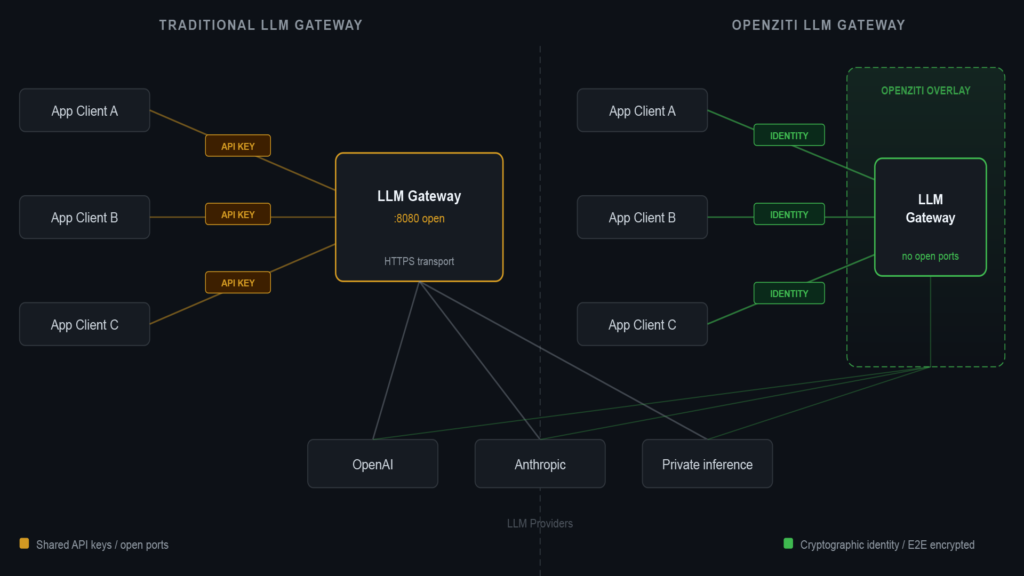
If you’re running multiple LLM providers and want a single API in front of them, you have options. This post compares open...
Why Digital Transformation Left OT’s Traditional “Broken” Networking in the Dust NetFoundry CEO Galeal Zino was recently interviewed by Larry O’Brien, VP...
Why Every DevOps Engineer Should Be Using Ziti Velocity vs security – why can we not have both? After working in the...
The Power of Dark Services with OpenZiti The recent OpenClaw vulnerabilities sent ripples through the cybersecurity community. Research from the SecurityScorecard STRIKE...
Jarvis or WannaCry, will the real OpenClaw please stand up? OpenClaw (FKA Clawdbot before legal pressure) broke the Internet. And it is...
In an era where digital operations define business success, companies need more than just connectivity—they need secure, controlled, and trusted connectivity. This...
As platform engineers, we are currently stuck between a rock and a hard place. Our internal developers want frictionless access to frontier...
After backpacking Sumatra for 28 grueling days, completely cut off from the rest of civilization, I arrived in Jakarta, Indonesia. There was a...